Attack Path Management, the BloodHound Enterprise Way
,
Join us as we break down the key concepts of Identity Attack Path Management.
In this interactive walkthrough, we will cover how BloodHound Enterprise approaches identification and elimination of attack paths. We’ll also discuss how security teams can operationalize continuous attack path mapping to measure impact and prioritize mitigation efforts to focus on protecting your most critical assets.
Some of the takeaways:
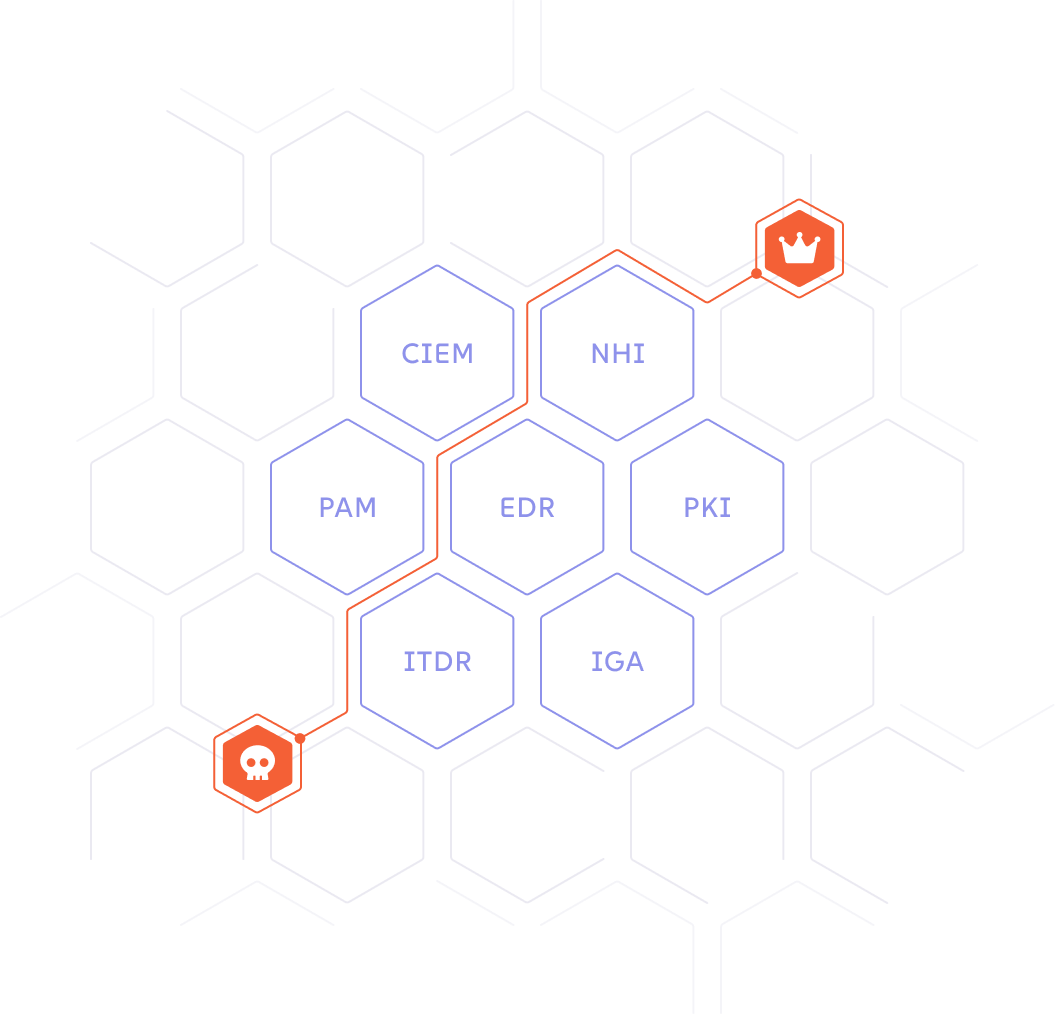
Attack Paths and the Attack Graph
What is an attack path and why do I care?
How does BloodHound Enterprise look for attack paths?
What are common attack paths in hybrid environments?
The BloodHound Enterprise Approach
Continuous/comprehensive attack path assessment
Quantifiable identity risk reduction
Prioritized remediation guidance/recommendation
Demo of BloodHound Enterprise
Register Today!
Featuring

Chris Abdala
SpecterOps
Sr Sales Engineer
Chris is a Senior Sales Engineer with 25+ years of experience across cybersecurity domains, including attack path management, network security, content security, and account takeover protection. He excels at bridging technical and business needs through pre- and post-sales engineering, security architecture, and strong customer engagement. Known for building trusted relationships, Chris delivers practical, effective security solutions with a hands-on approach.


